Passwordless authentication is a secure and user-friendly method of verifying identity that does not require the use of passwords. Instead, it uses other authentication methods like biometrics, devices, or actions to grant access to users. Traditional passwords have not provided any security and are difficult to remember, making them the primary target of cybercriminals.
In this blog, we explore the different types of passwordless authentication, how they work, and their implications for data security, including a comparison with multi-factor authentication (MFA).
Passwordless Authentication Benefits
- User Experience (UX)
Thanks to passwordless authentication, users no longer need to remember multiple passwords and secrets, streamlining the authentication process and eliminating password and secrets fatigue.
- Passwordless Authentication Reduces Risk
The fact that users can reuse passwords and have the capacity to share them with other people makes user-controlled passwords a significant security risk. Passwords are the root cause of other assaults, including credential stuffing, corporate account takeover (CATO), password spraying, and brute force attacks.
- Reduction in the Object’s Overall Acquisition Cost (TCO)
Eliminating passwords would minimise the number of support requests that need to be sent, allowing IT to focus more on solving actual issues. Passwords are costly, and they require ongoing maintenance from IT staff.
- IT Acquires Both Command and Visibility
When depending on passwords, frequent problems such as phishing, reuse, and sharing might arise; however, when using passwordless authentication, information technology can regain its objective of having total visibility over identity and access management – because there is nothing to phish, distribute, or reuse, the user is no longer the organisation’s wild card in terms of the identification system.
How does Passwordless Authentication Work?
Authentication methods that rely solely on username and password combinations are inherently vulnerable and can be easily compromised. For passwordless authentication, alternative elements such as biometrics, one-time passcodes, and cryptographic key pairs are required.
Passwordless Authentication is oftenused where users can establish a pair of public and private keys using a mobile app, browser plugin, or other tools. To access the private key, an authentication factor is required. Today’s digital workers rely on tools like Windows Hello for Business, FIDO keys, and the Microsoft Authenticator app.
Types of Passwordless Authentication
Discover the key types of passwordless authentication methods, from biometrics to hardware tokens, and understand how each provides a secure way to verify user identity.
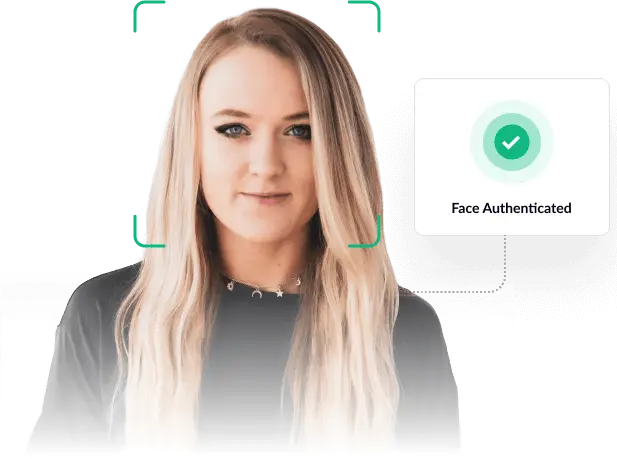
Biometric Authentication
- What It Is: Biometric authentication verifies individuals’ unique physical or behavioral characteristics. This includes fingerprints, facial recognition, iris scans, voice recognition, and heart rate patterns.
- How It Works: Biometric systems capture and store the user’s biometric data. When access is requested, the system compares the presented biometric data with the stored template to verify identity.
- Applications: Widely used in smartphones for unlocking and payment authorization, laptops for secure login, and high-security facilities for access control.
- Advantages: Tough to replicate or forge, offering high security. It also provides a quick and user-friendly authentication experience.
Magic Links
- What They Are: Magic links are unique, time-sensitive URLs sent to a user’s registered email address. Clicking the link grants the user access to the system or application.
- How They Work: The system generates a unique link associated with the user’s session. This link is sent to the user’s email, and upon clicking, the system authenticates the user based on the validity and uniqueness of the link.
- Applications: Commonly used for account verification, password resets, and secure logins for web applications.
- Advantages: Convenient and secure, as they are single-use and often expire after a short period. They also eliminate the need for users to remember passwords.
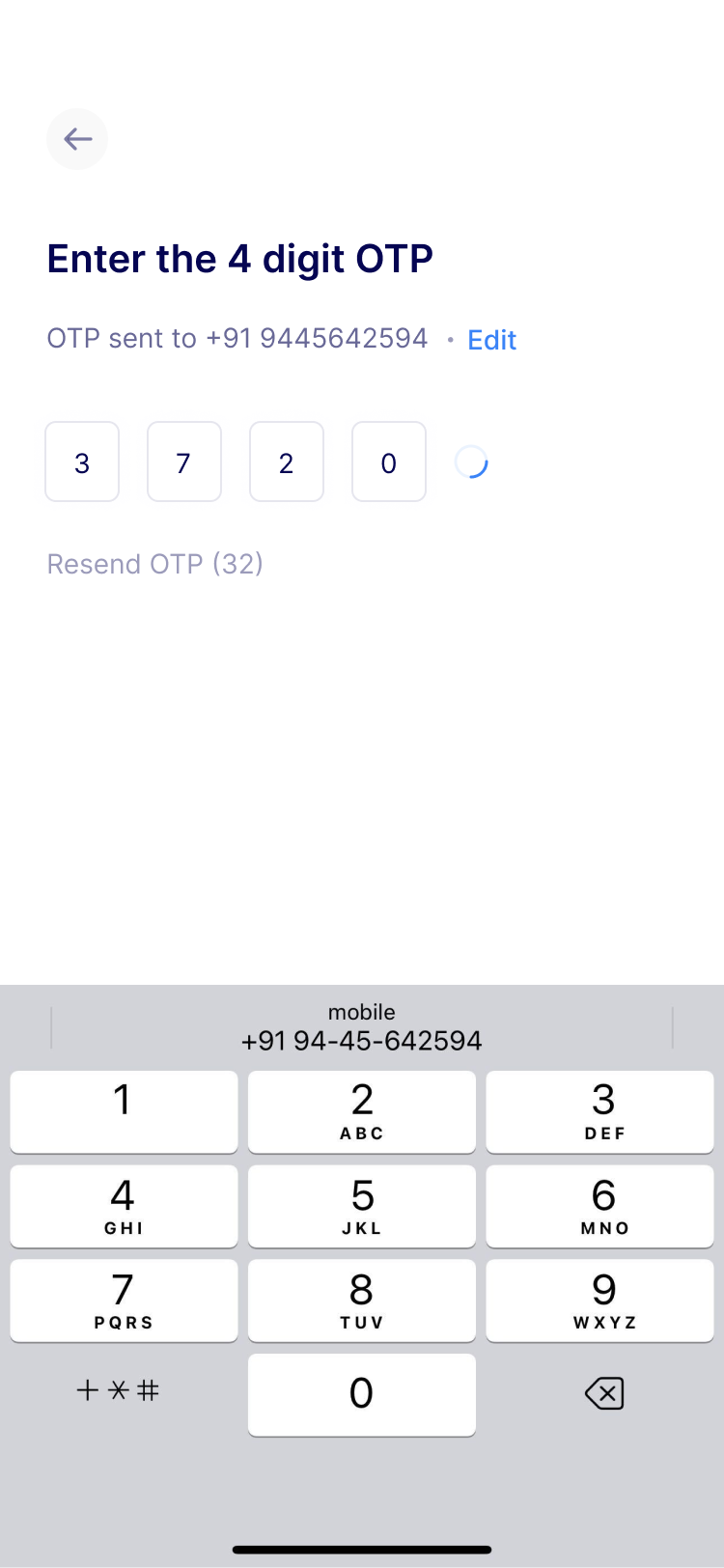
One-Time Passcodes (OTPs)
- What They Are: OTPs are single-use codes generated and sent to users via SMS, email, or an authenticator app.
- How They Work: The system generates a unique code sent to the user when requested access. The user then enters this code to gain access. The code is valid for a short duration, usually a few minutes.
- Applications: Widely used for two-factor authentication, banking transactions, and secure logins.
- Advantages: Adds an extra layer of security, as the code is transient and tied to the user’s device or email.
Hardware Tokens
- What They Are: Physical devices, such as key fobs, smart cards, or USB keys, that generate or store authentication information.
- How They Work: These devices generate a unique code at regular intervals or contain a cryptographic key used for authentication. The user presents the token or enters the code to verify their identity.
- Applications: Used in high-security environments, for accessing secure networks, and by individuals with heightened security needs.
- Advantages: Offers robust security, as it requires physical token possession. Not reliant on internet connectivity.
Data Security and Passwordless Authentication
Passwordless authentication redefines the data security landscape, offering a nuanced and advanced approach to protecting sensitive information. By eliminating the reliance on traditional passwords, it addresses a fundamental flaw in cybersecurity, eliminating risky password management, and reducing the risk of data breaches and cyberattacks that often exploit password vulnerabilities. This method introduces a higher level of security, utilizing biometrics, hardware tokens, or one-time codes, which are inherently more difficult to compromise.
Moreover, passwordless authentication streamlines the user experience, removing lax password management practices and the burden of creating, remembering, and managing complex passwords. This enhances convenience and encourages better security practices, as users are no longer tempted to reuse passwords or resort to easily guessable ones.
Multi-factor Authentication (MFA) vs Passwordless Authentication
Multi-factor authentication (MFA) and Passwordless Authentication are pivotal in bolstering security measures in our increasingly digital world. Understanding their roles and differences is key to navigating the evolving landscape of online security.
Fundamental Concepts
- MFA: Multi-factor authentication is a security system that requires users to provide two or more verification factors to gain access to a resource. These factors typically include something you know (password or PIN), something you have (a smartphone or security token), and something you are (biometric verification).
- Passwordless Authentication: As the name suggests, this method eliminates the need for passwords. Instead, it relies on alternative verification forms, such as biometrics, hardware tokens, or one-time codes.
Security Dynamics
- MFA: The strength of MFA lies in its layered approach. Unauthorized access is still difficult even if one factor is compromised due to the additional verification requirements.
- Passwordless Authentication: This approach directly addresses the vulnerabilities associated with passwords. Removing passwords from the equation eliminates a common attack vector.
User Experience
- MFA: While MFA enhances security, it can sometimes lead to a more cumbersome user experience, especially if the process is time-consuming or complex.
- Passwordless Authentication: Generally offers a more seamless and user-friendly experience. Users don’t have to remember complex passwords; authentication can often be completed with a simple action like a fingerprint scan or clicking a link.
Implementation and Compatibility
- MFA: This can be implemented in various environments and is compatible with various systems. However, it requires users to manage multiple authentication factors.
- Passwordless Authentication: Implementation can be straightforward, especially with modern infrastructure. However, it may require updates or changes to existing systems to accommodate passwordless methods.
Security vs. Convenience Trade-off
- MFA: Sometimes seen as a trade-off between security and convenience. More factors can mean higher security but potentially at the cost of user convenience.
- Passwordless Authentication: Aims to offer both security and convenience. However, its effectiveness can depend on the specific method used and the context of its application.
Adaptability and Future Trends
- MFA: Continues to evolve, integrating new forms of authentication factors.
- Passwordless Authentication: This is seen as a forward-looking approach, aligning with trends towards greater simplicity and user-centric security.
How to Implement Passwordless Authentication
Passwordless authentication is a versatile and robust solution for securing digital interactions across numerous industries. Its ability to adapt to different environments—from corporate to healthcare and from banking to consumer electronics—demonstrates its potential to streamline the user experience and significantly bolster security measures.
As we embrace digital transformation, adopting passwordless authentication methods will likely become a standard, reshaping how we think about and implement security in our daily digital routines. For more informational content, head over to our blogs!






